Security audit and penetration-testing web app
A centralised web portal for providing the results of security audits to customers.
"Codevate really understood what we wanted to achieve and the feedback from our clients, prospects and even competitors has been excellent. We have some big plans for the portal that they helped us bring to life and we'll be continuing to use Codevate on that journey. I can't recommend them enough!"
Digitising and automating business processes
Our client performs security audits and penetration tests on their customer's software and network infrastructure. Previously, PDF reports were sent directly to clients over email. This made versioning difficult as every time there was a change, the report would need to be updated and sent around. It also meant that customers had to wait until a report was completely before they could start patching vulnerabilities that had been identified.
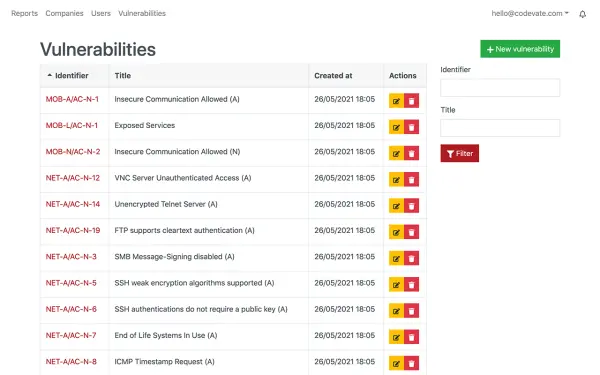
We developed a web-based portal to centralise the business processes around reporting. There were several areas where internal operational efficiency could be improved. Testers would often report the same common vulnerabilities on multiple projects - by implementing a shared vulnerability database, much time could be saved.
After a successful launch of the new web portal, our client now has a unique advantage over their competitors. The new portal greatly increases productivity and improves the customer experience.
Want to build your own web portal?
Services delivered
Technologies used
- PHP - Symfony
- TypeScript - React
- PostgreSQL database
- AWS cloud infrastructure
Highlights of the security audit portal
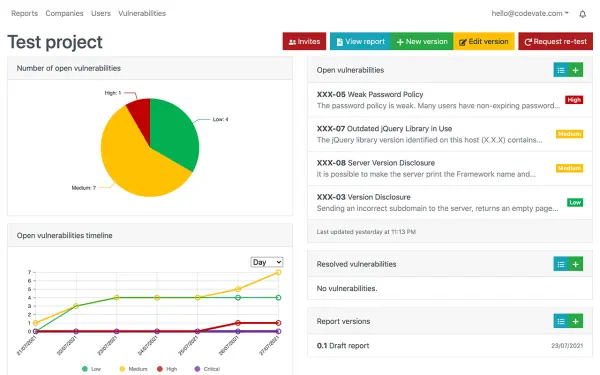
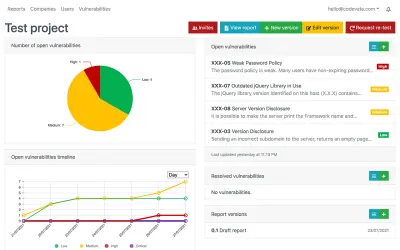
Audit overview dashboard
- Visual dashboard that summarises audit status at a glance, allowing actions to be taken more quickly - reducing the risk of damage
- Charts highlight unresolved vulnerabilities by severity and over time, aiding performance metrics
- Status lists show open and resolved issues with context - quickly showing what actions need to be taken
- Enables fast response to risks, closing the security feedback loop
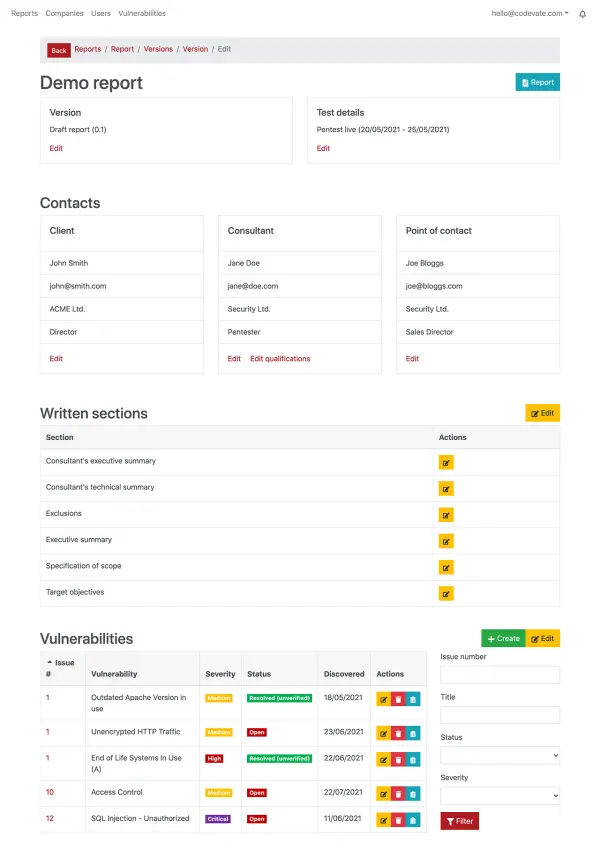
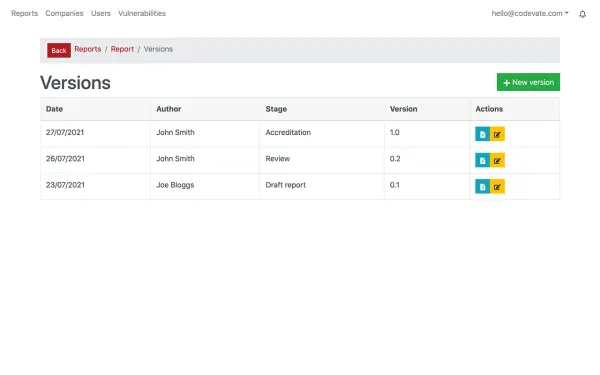
Interactive report builder
- Interactive report builder streamlines audit workflows and removes the need for manual formatting - ensuring consistent quality and branding
- Step-by-step wizard makes collaborative report writing easy for both consultants and testers
- Testers can report vulnerabilities intuitively as part of the audit workflow, without having to worry about formatting and sharing a document
- Automatic report generation produces multiple report types instantly, saving time and effort
Behind-the-scenes and other top features
Not all heroes wear capes. These behind-the-scenes features don't have screenshots, but form an important part of the project.
Customer accounts
Tighten the feedback loop and provide a better customer experience.
PDF report generation
Consistently format branded PDFs that are readable on any device.
Multifactor authentication (MFA)
MFA via SMS, email and phone to secure user accounts and protect sensitive information
Notifications centre
Kee pall parties up to date with important updates in the system
Want to develop an app or cloud portal like this?
"Codevate really understood what we wanted to achieve and the feedback from our clients, prospects and even competitors has been excellent. We have some big plans for the portal that they helped us bring to life and we'll be continuing to use Codevate on that journey. I can't recommend them enough!"
- 100% UK-based
- Complimentary scoping call
- At-a-glance feasibility analysis
- No obligation high-level proposal
- Work with an expert to evolve your idea
Project outline: building the web portal
Our client performs security audits and penetration tests on their customer's software and network infrastructure. These audits can span from a few days, to months or more.
Before we developed this software, reports were being produced in Word, and findings were communicated via email. This approach was limiting their ability to scale the company. Human error, lack of efficiency, and organisation were some of the biggest pain points. Off-the-shelf software didn't have the capability to fit seamlessly into our client's processes, so bespoke software was the best way to go.
Our solution
We designed and developed this centralised system that encapsulated the main report-writing processes. The goal was to add as much automation to our client's workflow as possible — increasing productivity whilst improving the customer experience. The core feature is the interactive report builder, which pulls in information entered into the system and generates branded digital reports.
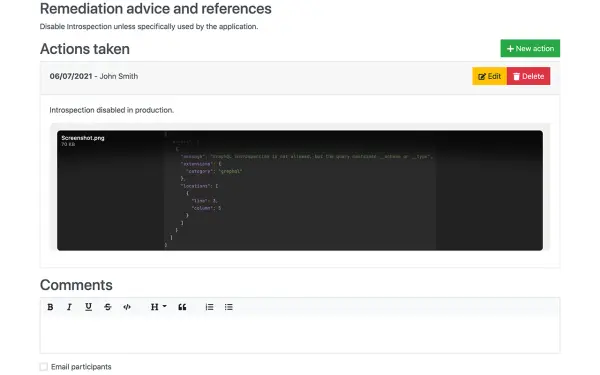
Customers are given access to their report via the web portal, and have the option to download a PDF copy. They also have the ability to report remedial actions that they have taken. This in turn allows customers to keep their own audit trail, and manage risks appropriately.
Delivering the new software
The new bespoke solution has put the company on a growth path — taking the company to the next level. All information is now centralised, helping to prevent important information and actions being lost in email threads. Initial feedback has shown that reports can be produced in a shorter amount of time, giving the client opportunities to increase profit margins.
The improved communication is closing the feedback loop with customers, providing a better experience and potentially increased repeat business. The new software provides a positive unfair advantage over their competitors, who may not be able to match the new service offering.
Finally, as client reports are now fully accessible via the web portal, reports are kept up-to-date in real time — a major advantage over printed reports, and a significant green advantage for the project.
Want to build your own web portal?
Looking to develop software that's greater than the sum of its parts?
Send us a message